...
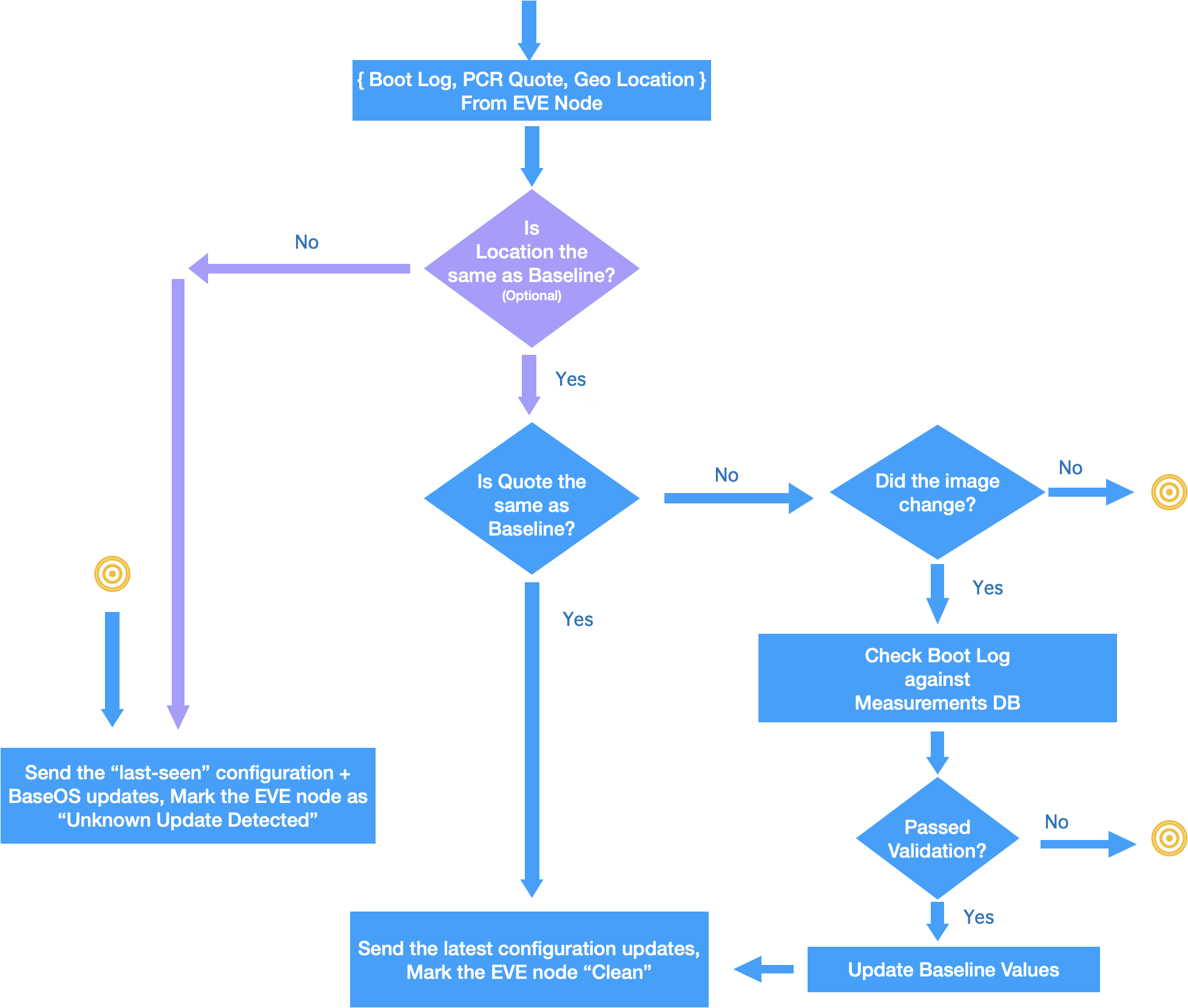
Fig1. Role of ZedCloud as the Remote Attestation Server
Solution Overview
- To identify if the software running on EVE node is the intended software, a A new device flagstate, “Unknown Update Detected” (Abbreviated as UUD) will be introduced in EVC, to indicate to the user in EVC that software running on a given device is not one of the intended/certified imagesAnother new device flag, “Unknown Movement Detected” (Abbreviated as
- UMD) will An optional feature, "Location-Lock" may be introduced in EVC, to indicate that a change in the location of the device has been detected. This will be an optional “Location-Lock” feature. Admin can enable this feature if the EVE node is not a mobile device, and the location for the same is not expected to change (Geo location of the EVE node has been changed since last(indicating a potential physical compromise)Device reports PCR Quote/Geo-Location value along with config request (with an appropriate nonce, to force the quote to be current)additionally check the Geo-Location reported by device, and flag if the location has changed since its last-seen location. This feature may be critical in some deployments, where a given EVE node may be mounted permanently, and any change in its physical location should be flagged, and optionally considered along with software measurements to conclude if the EVE node is trusted. In this regard, another new device flag, “Unknown Movement Detected” (Abbreviated as UMD) will be introduced in EVC, to indicate that a change in the location of the device has been detected.
- EVC maintains a central database of all the supported EVE software images, and their hash values, indexed with the EVE image version tag
- EVC also maintains a central database of all the mostly used BIOS firmware images, their signatures, and the certificate provided by the BIOS vendor for validating the signatures, indexed by a combined tag of BIOS version string + Manufacturer
- On every reboot, EVE sends PCR quote to EVC, along with optional Geo-Location information, along with its EVE image version and BIOS firmware version.
- After normal reboot After normal reboot operation of EVE, EVC checks PCR Quote against the baseline value. If there is a change, the edge-node is marked as “UUD”. If "Location-Lock" feature is enabled and the location of the EVE node has changed, EVE node is marked "UMD"
- After EVE software upgrade, it is expected After EVE software upgrade, it is expected that the baseline value will change for the PCR values. However, after comparing the reported values with the expected values(since EVC knows about the new image version and its hash values), EVC makes a decision: If the reported values match, the baseline for the EVE node is updated. If they don’t, it is a UUD detection. Optionally, if administrator enables “Location-Lock” feature, Geo-Location of the device will also be included in the checks, before sending the latest configuration.
- If edge-node is in “UUD” or "UMD" state, only the “last-seen” EVE configuration, along with the latest baseOS configuration is sent as config request response, all other new configuration items will be omitted in config response. This is to protect any new sensitive images/credentials from getting exposed to the compromised device. Here "last-seen" refers to the configuration last received by EVE from EVC.
- If EVE node is not in “UUD" or "UMD" If EVE node is not in “Unknown Update Detected” state, all the latest configuration items are included.
- Optionally, if administrator enables “Location-Lock” feature, Geo-Location of the device will also be included in the checks, before sending the latest configuration.
- Frequency of attestation: EVE node will be required to periodically attest EVE node will be required to periodically attest itself via attestation requests. The interval is fixed to be every 4 hours, or whenever the device connects back to the cloud again, or after the next reboot, whichever is earlier.
- Also, for every configuration request, EVE node is required to send a token string, known as “Integrity Token”. This token is sent during attestation requests, and if the attestation is successful, the provided token value is locked against the EVE node. EVE node is required to keep this token under /persist/vault, and produce this token with every config request.
- This 4 hours is a tentative interval, and can be changed based on deployment requirements.
- If EVE reboots with a different software image from the configured version, EVC should be able to detect as quickly as possible and force attestation. To this effect a new token is introduced, called "Integrity Token". This token is a random nonce that will be stored in EVE under an encrypted folder. The master-key to decrypt this folder will be sealed against the TPM PCRs. Therefore, if EVE reboots with a different software, unsealing of this key will fail, and hence the new software will not be able to recover the Integrity Token inside it.
- This token is sent during attestation requests, and if the attestation is successful, the provided token value is locked against the EVE node.
- Every configuration request from EVE will include this Integrity Token. If there is a token mismatch, HTTP code 401 - Unauthorized will be sent to the device as the response, indicating that device should do re-If there is a token mismatch, HTTP code 401 - Unauthorized will be sent to the device as the response, indicating that device should do re-attestation. This mechanism is put in place as a quick check against the software state. By storing the token inside a secure folder with key sealed against PCR values, if EVE fails to produce this token, one can consider this as a condition to re-trigger full attestation immediately, instead of waiting for the next 4-hour slot for regular attestation.
Fig 2. Remote Attestation Flow in EVC
...
- To establish a baseline, the following is proposed:
EVE device is onboarded in on-boarded in a trusted environment, usually in a manufacturing/supply chain setup (or Intel SDO) - When EVE is onboarded for on-boarded for the first time, during device-certificate registration, the PCR values coming out of the EVE node will be taken as the baseline for that device. Any change in the PCR value (other than during an EVC-driven upgrade, explained below) after will be flagged as UUD, and unless the user marks it as legal/accepted, the EVE node will remain in the UUD state.
- If the enterprise account is a manufacturing account, then geo-location will be exempted in calculating the baseline.
- When the EVE node comes online for the first time in a non-manufacturing enterprise, geo-location of the EVE node will be taken and will be frozen as the baseline value for geo-location.
- In case of mobile gateways, there will be an option to turn-off Geo-Fencing(i.e. Locking of Geo location)
...