...
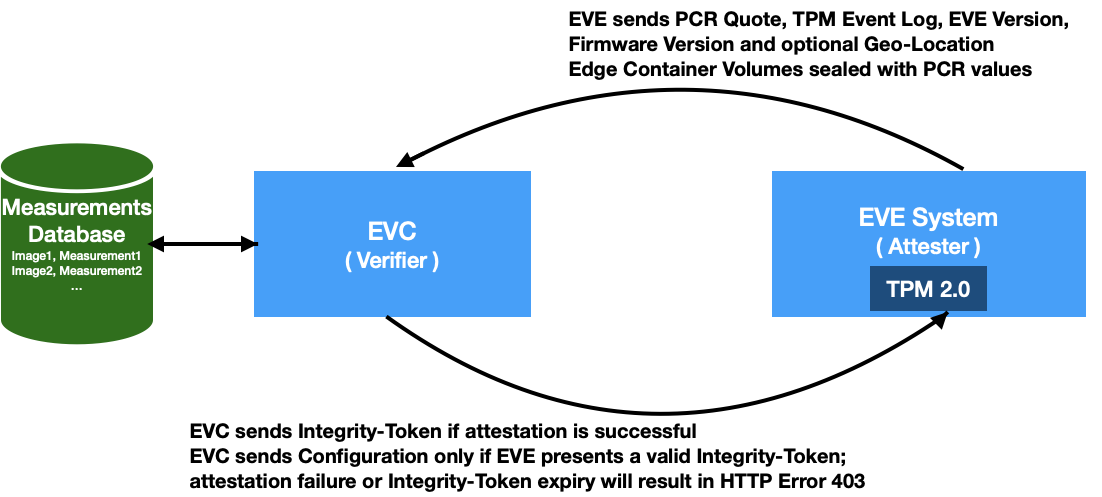
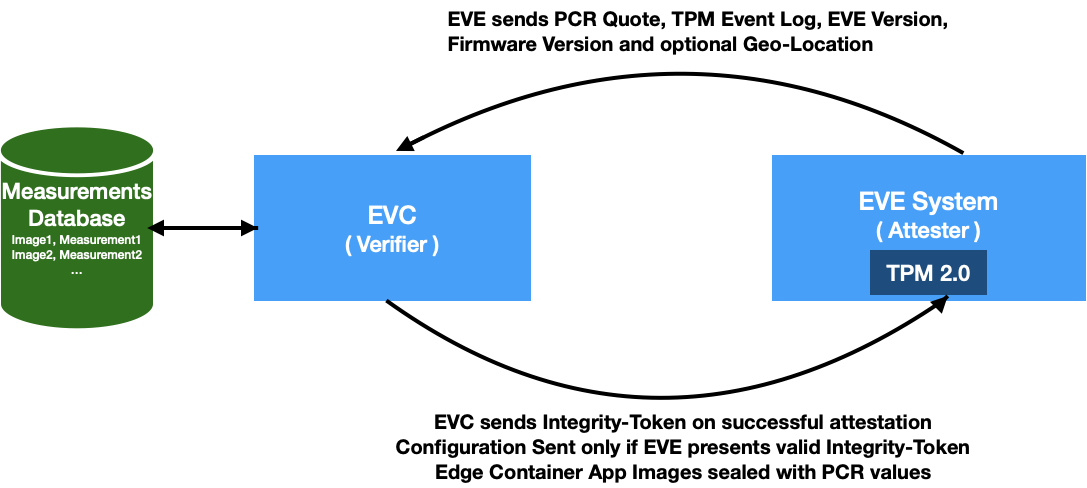
Based on the above constructs, we present a solution to measure and attest software integrity of EVE node. Just for recap, EVE is the open-source software from LF-Edge for Edge Virtualization, running on IoT Edge gateways. EVC is the controller for managing these EVE instances. Adam under LF-Edge is an open source implementation of one such EVC. The APIs between EVE and EVC are specified in EVE API specification. In the context of remote attestation, the EVC is the attesting authority and EVE reports its measurements for attestation.
Fig 1. Role of EVC as the verifier, and EVE as the attester
...
- A new device state, “Unknown Update Detected” (Abbreviated as UUD) will be introduced in EVC, to notify that measurements of software running on a given device didn't match expected measurements.
- EVC maintains a central database of all the supported EVE software images, and their hash values, indexed with the EVE image version tag
- EVC also maintains a central database of mostly used BIOS firmware images, their signatures, and the certificate provided by the BIOS vendor for validating the signatures, indexed by a combined tag of BIOS version string + Manufacturer
- On receiving attestation request EVE, attestation service module checks PCR Quote against the baseline value. If there is a change, the EVE node is marked as “UUD”. When there is no software change, the PCR quote is expected to be the same across reboots. However, after an EVE software upgrade, it is expected that the baseline value will change for the PCR values. However, after comparing the reported values with the expected values(since EVC knows about the new image version and its hash values), EVC makes a decision: If the reported values match, the baseline for the EVE node is updated. If they don’t, EVE node is marked as UUD.
- An optional feature, "Location-Lock" may be introduced in EVC, to additionally check the Geo-Location reported by device, and flag if the location has changed since its last-seen location. This feature may be critical in some deployments, where a given EVE node may be mounted permanently, and any change in its physical location should be flagged, and optionally considered along with software measurements to conclude if the EVE node is trusted. In this regard, another new device flag, “Unknown Movement Detected” (Abbreviated as UMD) will be introduced in EVC, to indicate that a change in the location of the device has been detected.
- If EVE node is not in “UUD" or "UMD" state, EVC includes all the latest configuration in reply to config request from EVE.
- If edge-node is in “UUD” or "UMD" state, any config request from EVE will be responded with response code 403 - Forbidden. This is to protect any new sensitive images/credentials from getting exposed to the compromised device. The response from EVC in such cases will carry an error code to indicate that there was an attestation failure, and hence partial configuration is being sent. EVE, upon receiving such error codes MUST schedule re-attestation immediately.
- If EVE reboots with a different software image from the configured version, EVC should be able to detect as quickly as possible and force attestation. To this effect a new token is introduced, called "Integrity Token". This token is a random nonce that will be stored in EVE under an encrypted folder. The key for the encrypted volume the Volume Storage Key to decrypt this folder will be sealed against the TPM PCRs. Therefore, if EVE reboots with a different software, unsealing of this key will fail, and hence the new software will not be able to recover the Integrity Token inside it. This token is sent during attestation requests, and if the attestation is successful, the provided token value is sealed against PCR values. This is usually implemented by storing the token inside an encrypted folder, with the key for the encrypted volume Volume Storage Key protected by TPM with Seal operation.
- Every configuration request from EVE will include this Integrity Token. If there is a token mismatch, HTTP code 403 - Forbidden will be sent to the device as the response, indicating that device should do re-attestation.
- Frequency of attestation: EVE node will be required to periodically attest itself via attestation requests. It is up to the EVC to schedule the frequency of attestation. Whenever EVC replies with Error 403, EVE MUST re-attest. EVC can trigger this either periodically (say every few hours) or when it sees any discrepancy in the Integrity-Token.
...
All the ECO Volumes would be inside the encrypted folder (/persist/vault), with the key for the encrypted volume Volume Storage Key sealed inside TPM, against a set of PCR values. Without access to this key for the encrypted volume, the encrypted folders can not be accessed. Essentially this means that the contents of the user-provisioned volumes are sealed against PCR values.
...
To implement this, ECO volumes would be inside the encrypted folder (/persist/vault), with the key for the encrypted volume Volume Storage Key sealed inside TPM.
To provide some flexibility to the EVE node administrator, when deploying ECOs on the EVE platform, there will be 3 security modes for app deployment:
...
- Device-steps starts client.go (the provisioning client) which will check and do the following:
- If EVC is not reachable, uses certificates from the last download
- If EVC is not reachable, uses UUID already present in /config/uuid
- Device-steps starts Vault Mgr
- Vault Mgr retrieves the master decryption key from TPM with Unseal operation. Unseal is successful since the PCR values are the same since last reboot.
- Unlocks /persist/vault with the key for the encrypted volumeVolume Storage Key.
- Publishes vault status (unlocked)
- Device-steps starts TPM mgr
- TPM manger retrieves the attestation certificate and publishes to Zedagent
- Waits for Quote requests on pubsub channel from Zedagent
- Device-steps starts Zed Manager, Domain Mgr microservices - these services are responsible for launching the ECOs
- Device-steps starts Zedagent (and Zedagent starts 3 concurrent tasks: attest, info and config)
- Configuration task, since EVC is not reachable, uses the configuration from the last download, and publishes to Zed Mgr and Domain Mgr
- Since the Vault is unlocked, Domain Mgr can access Edge App Images, and hence launches the ECOs.
...
- Device-steps starts client.go (the provisioning client) which will check and do the following:
- If certificates from EVC are not yet fetched, fetches them
- Retrieves UUID from EVC
- Device-steps starts Vault Mgr
- Vault Mgr tries to retrieve the master decryption key from TPM with Unseal operation, and Unseal operation fails since the PCR values have changed
- Publishes vault status (as "locked")
- Waits for Integrity-Token and/or key for the encrypted volume from EVC - it will block here forever
- Device-steps starts TPM mgr
- TPM manger retrieves the attestation certificate and publishes to Zedagent
- Waits for Quote requests on pubsub channel from Zedagent
- Device-steps starts Zedagent (and Zedagent starts 3 concurrent tasks: attest, info and config)
- Device-steps starts Edge App microservices - e.g. Domain Mgr
- Attest task requests for a nonce from EVC (to prepare PCR quote)
- Attest task sends the nonce back to TPM Mgr and waits for PCR quote
- Attest task, once notified about the quote readiness, creates a random nonce value for Integrity-Token
- Attest task sends { Quote, Location, Event Log, Integrity-Token, Image Version } to EVC
- EVC, since the quote is different, tries to compare EventLog entries with its known hashes against the version reported. Since the PCR values are different, there will not be match, unless Admin has uploaded measurements for this new version. Assuming that Admin is yet to upload, attestation request will fail here.
- EVC sends an error back to EVE, to retry attestation.
- In the mean time, configuration task keeps requesting config from EVC (expected to fail till attestation goes through).
- EVC replies to configuration request with HTTP Error Code 403 - Forbidden. Indicates attestation failure (due to no or invalid Integrity Token)
- Config task communicates to Attest Task to re-trigger attestation
- Admin uploads measurements for the new image version
- The next attestation request is matched successfully against the uploaded measurements
- EVC approves the attestation request, and responds back with the key for the encrypted volume Volume Storage Key (encrypted with TPM key) for the EVE node, and also saves the Integrity-Token supplied in the attestation request
- Vault Mgr
- picks up the key for the encrypted volumeVolume Storage Key
- unlocks vault
- populates Integrity-Token approved by EVC inside /persist/vault/itoken
- Publishes new vault status (unlocked) to all the microservices
- The next configuration request picks up the new Integrity Token, and sends configuration request along with this Integrity-Token
- EVC verifies that Integrity-Token matches with its copy, and approves configuration request and responds with the latest configuration.
- Domain Mgr notices the new vault status (unlocked) from Vault Mgr , and latest configuration from ZedAgent, and starts the Edge Apps
- Info task reports the encrypted key for the encrypted volume back to EVC, for backup purposes
...
- Device-steps starts client.go (the provisioning client) which will check and do the following:
- First fetches EVC Certificates
- Registers the device certificate
- Retrieves UUID from EVC
- Device-steps starts Vault Mgr
- Vault Mgr creates new vault: /persist/vault
- Seals the key for the encrypted volume Volume Storage Key into TPM with PCR values
- Publishes vault status (unlocked)
- Waits for Integrity-Token from zedAgent
- Once received, copies the new Integrity-Token to /persist/vault/itoken file
- Device-steps starts TPM mgr
- TPM manger retrieves the attestation certificate and publishes to Zedagent
- Waits for Quote requests on pubsub channel from Zedagent
- Device-steps starts Zedagent (and Zedagent starts 3 concurrent tasks: attest, info and config)
- Attest task,
- picks up the attestation certificate and publishes to EVC
- requests for a nonce from EVC (to prepare PCR quote)
- sends the nonce back to TPM Mgr and waits for PCR quote
- Once notified about the quote readiness, creates a random nonce value for Integrity-Token
- Sends { Quote, Location, Event Log, Integrity-Token, Image Version } to EVC
- EVC, if key for the encrypted volume is not found for the EVE, approves the PCR quote as the baseline
- If Location-Lock is enabled, location is also approved as baseline (provided the EVE device is not in manufacturing account)
- In the mean time, configuration task keeps requesting config from EVC (expected to fail till attestation goes through)
- Attest task, once attestation request is approved, gets the key for the encrypted volume Volume Storage Key and Integrity-Token and passes it to Vault Mgr
- Config task now picks up the right Integrity-Token and Config request is now accepted by EVC, and full configuration is sent back
- Info task reports the encrypted key for the encrypted volume back to EVC, for backup purposes
...
When EVE goes through a software upgrade, the PCR values will change depending on what is new in the upgraded version. However, during the upgrade window, an attacker might boot a different software as well, and try to present the compromised software as the upgraded version of EVE. Therefore, it is important that we measure the boot sequence after the upgrade and validate that the new software is indeed the new image that was pushed by the EVC. This is done through the following steps:
- EVE encrypts the key for the encrypted volume using Volume Storage Key using a TPM-based key, and sends it to EVC. EVE can send this information when the key for the encrypted volume Volume Storage Key is created for the first time, and also can include this in the periodic info message. Sending this in periodic info message also provides additional facility of rotating the key if required.
- After the upgrade, the EVE software presents the new Event Log, along with the PCR Quote. As mentioned earlier, the PCR Extend operations are recorded in a table called TPM Event Log Table. This is sometimes also called the Boot Log.
- First, EVC repeats the transactions mentioned in the Event log, and the final PCR as computed from the Event Log should match the PCR Quote. If they don’t match, then Event Log can’t be trusted(say it was manipulated), and the EVE node is marked as UUD. Please note: Event Log is stored in system memory and PCR Quote is generated by TPM. So PCR quote is the source of truth, pinned to HRoT.
- Secondly, if PCR Quote matches the Event Log, then Event Log entries are compared between old Event Log and the new Event Log, and the differing entries are extracted
- EVC maintains a central database of all the supported EVE software images, and their hash values, indexed with the EVE image version tag
- EVC also maintains a central database of all the BIOS firmware images, their signatures, and the certificate provided by the BIOS vendor for validating the signatures, indexed by a combined tag of BIOS version string + Manufacturer
- The differing values are compared against acceptable values stored against the given image version. Additionally, If admin has enabled “Location-Lock” feature, additionally the geo-location reported by the device is checked as well. The Geo-location reported by the device can be trusted if the software state (established through PCR quote) can be trusted.
- If the PCR quote and the optional Geo-Location check pass, the encrypted key for the encrypted volume is given back to the EVE node. EVE decrypts the key for the encrypted volumeVolume Storage Key, and unlocks the vault with the key for the encrypted volume. The key for the encrypted volume Volume Storage Key. the Volume Storage Key is now sealed into the TPM, against the current PCR values.
- User will have an option to override the attestation decision taken by EVC, through a configuration in EVC portal, against the EVE node
...
| URI | Type | Request Contains | Response Contains | Functionality |
|---|---|---|---|---|
/api/v2/edgeDevice/uuid | POST | Empty payload, with just AuthContainer | UUID of the device or Error 404 | Return UUID of the device, based on device certificate present in AuthContainer. So far, EVE has been re-using /api/v2/edgeDevice/config to get UUID of the device in the initial stages of starting EVE services. But with measured boot and remote attestation, configuration is sent to device only when device is attested for software integrity (which happens later as part zedAgent). Therefore, it may be observed that for getting UUID, fetching the whole configuration (which requires attestation now) would be an overkill, and hence the need for this new lightweight URI. The proposed /uuid is lightweight URI that responds with a single field that contains the UUID of the device. If the device is not known, Error 404 is sent. |
| /api/v2/edgeDevice/{uuid}/attest SubType ATTEST_REQ_CERT | POST | X.509 Certificate signed by Device Certificate | No Response Payload, only the standard HTTP status codes | To send attestation certificate. This certificate is used to validate signature of the PCR Quote. This certificate is different from device certificate and ECDH certificate. The cert type for this will be set to CERT_TYPE_DEVICE_RESTRICTED_SIGNING. For more details, please refer this section of API documentation |
| /api/v2/edgeDevice/{uuid}/attest SubType ATTEST_REQ_NONCE | POST | Empty payload, with just AuthContainer | Nonce Value | To request a nonce from controller. This nonce will be included while generating PCR Quote. This will trigger re-fetching of nonce from device. For more details, please refer this section of API documentation |
| /api/v2/edgeDevice/{uuid}/attest SubType ATTEST_REQ_QUOTE | POST | PCR Quote, Event Log, Integrity Token, Image Version, Firmware Version, Nonce used | SUCCESS or FAILURE. If FAILURE Sub-code indicates whether there is a nonce mismatch mismatch. Also carries Integrity-Token Value, and the encrypted Volume Storage Key | To send { PCR Quote, Event Log, Integrity Token, and Image version } for attestation. If attestation result (PASS/FAIL) is sent back as response. If attestation is successful, EVC will cache the Integrity Token , and the encrypted Volume Storage Key in the response. The next config request should contain the same Integrity-Token as proof of access to the Vault.
For more details, please refer this section of API documentation |
| /api/v2/edgeDevice/{uuid}/config | POST | Hash of last configuration received, Integrity Token as proof of access to the Vault | Full configuration in case of proper Integrity Token, Error 403 if there is a Integrity-Token mismatch | Device will include Integrity-Token and hash of the last-received configuration in the request. Controller will run a periodic time check, and attestation has to be redone periodically at these intervals. |
...